I Thought I Understood Backend Development — I Didn’t
For a long time, I walked around with a dangerous level of confidence.
I could spin up a Node server in my sleep. I could write a schema, wire up some REST endpoints, connect a database, and deploy the whole thing to the cloud. When I hit the endpoint in Postman and saw that green 200 OK, I felt like a wizard.
"Backend is easy," I told myself. "It’s just plumbing. Move data from A to B. Don't let it leak."
That belief held up surprisingly well—as long as I was building demos, tutorials, and side projects that nobody used.
Then I tried to build a real system.
It was a platform meant to handle actual transactions, real user roles, and background processing. It wasn't Facebook scale, but it had users who would notice if things broke.
And things did break.
They didn't explode in a ball of fire. They didn't throw clear error messages. They broke in subtle, insidious ways that made me question my sanity.
That project taught me the difference between knowing syntax and understanding systems. Here is how my confidence fell apart, piece by piece.
1. The Auth Illusion: It’s Not Just a Checkbox
In every tutorial I’d ever watched, authentication was treated like a feature you simply install.
- Import library.
- Add
verifyTokenmiddleware. - Done.
So, that's what I did. I built a system with "Admins" and "Users." I tested it locally: I logged in as an Admin, I could delete things. I logged in as a User, I couldn't. Ship it.
The "Ghost" Session
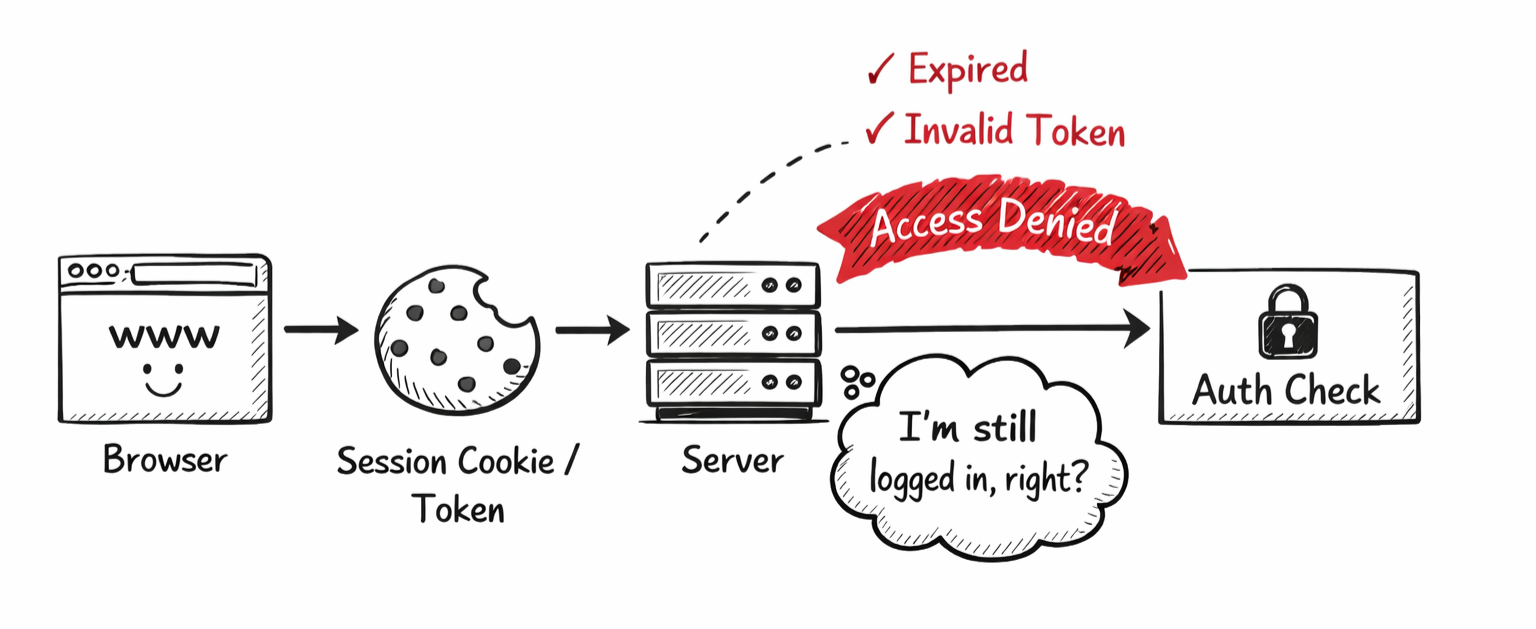
Three days into production, I got a weird report. A user claimed they were seeing data that didn't belong to them.
I checked the code. The middleware was there. The logic looked perfect.
What I hadn't accounted for was the state of trust.
I was using cookies. I assumed that if a cookie existed, the user was valid. But I hadn't thought about what happens when I ban a user on the server. The banned user still had a valid cookie on their browser. My middleware checked “Is this token valid?” (Yes, cryptographically it was), but it didn't check “Does this user still exist and do they still have rights?” on every single hop.
I treated Auth as a gate you pass through once. Reality taught me that Auth is a conversation that happens on every single request.
If you don't design for the edge cases—expired tokens, banned users, stale permissions—you aren't building a secure system. You're just building a system that hasn't been hacked yet.
2. The Database Betrayal: It Does What You Say, Not What You Mean
This was the most humiliating part.
I was building a simple inventory feature. Logic:
- Read the current stock (e.g., 10 items).
- Subtract 1.
- Save the new stock (9 items).
Simple, right? It worked perfectly when I clicked the button.
The Race Condition
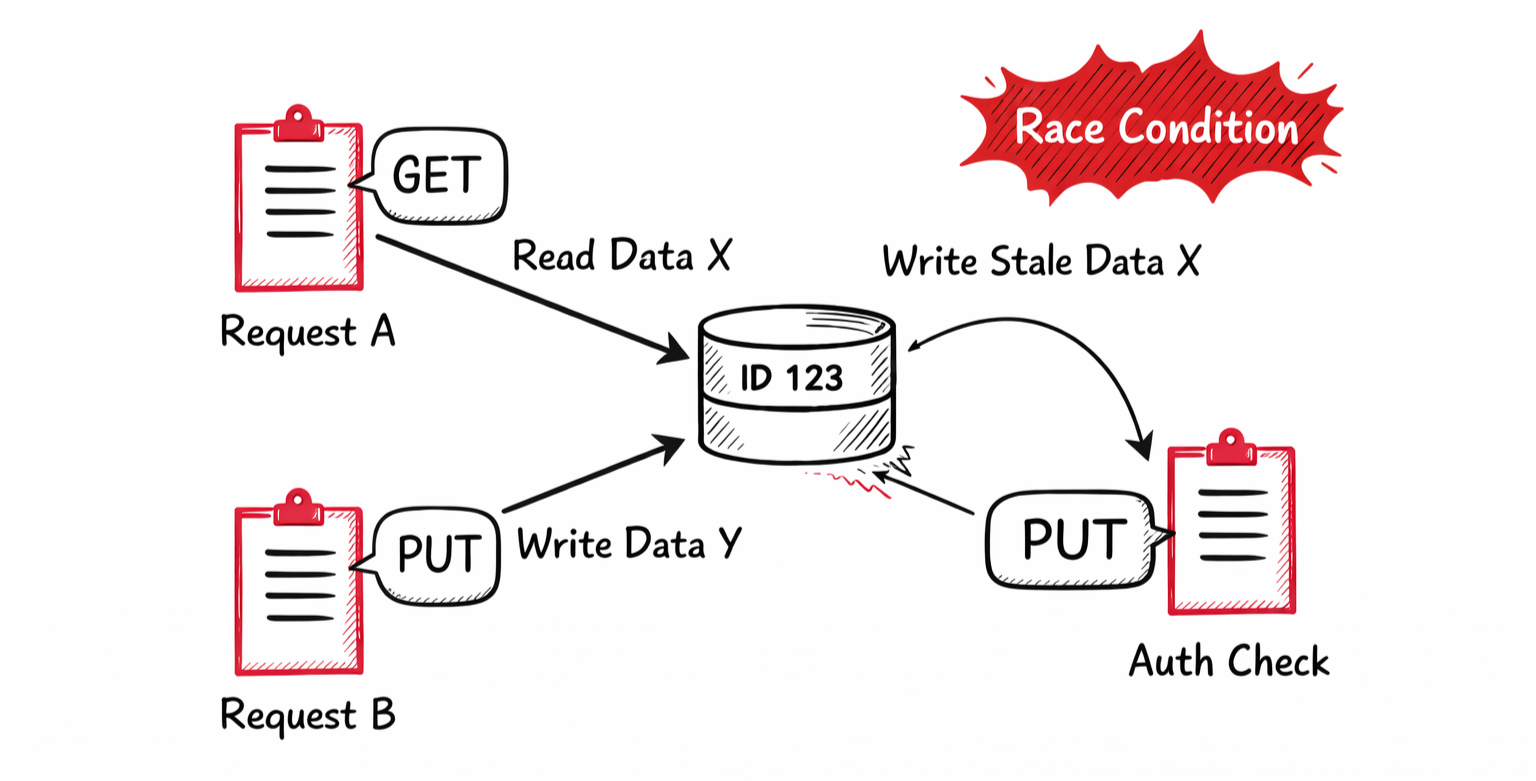
Then, we had a moment where two users tried to buy the last item at the exact same second.
- User A requested the item. The server saw Stock: 1.
- User B requested the item. The server saw Stock: 1 (because User A hadn't finished writing yet).
- User A bought it. Stock became 0.
- User B bought it. Stock became 0.
The database didn't throw an error. It didn't crash. It happily sold the same item twice.
I stared at the logs for hours. "But I wrote the logic!" I yelled at my monitor.
That’s when I realized: The database is a literalist genie.
It executed my commands exactly as they arrived. I was coding as if my server processed one person at a time. But in the real world, requests happen in parallel.
If you aren't thinking about transactions, locking, and concurrency, you aren't writing backend code. You're writing a script that only works when nobody is using it.
3. The Async Trap: Complexity Doesn't Disappear, It Migrates
After the database fiasco, I tried to be "smart" about performance.
"Sending emails is slow," I thought. "I'll push that to a background queue. The user gets an instant response, and the worker handles the email later. Pure efficiency."
I felt like a senior engineer. I was using Redis! I was using Workers!
The Zombie Task
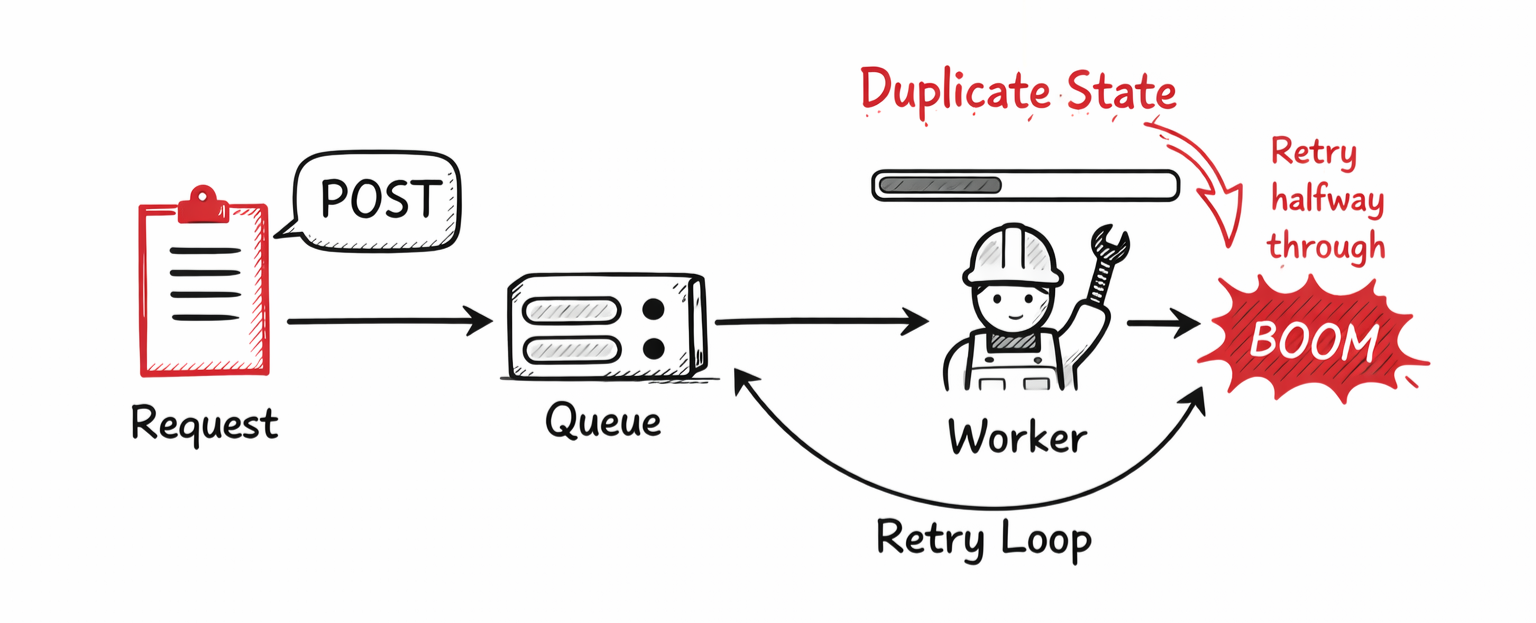
Then the email service had a brief outage. Just 5 minutes.
My worker tried to send an email, failed, and—because I configured it to be "reliable"—it retried. And retried. And retried.
But I hadn't made the task idempotent.
When the email service came back up, my worker had queued up hundreds of "retry" attempts. One poor user received the same "Welcome to the Platform!" email 40 times in ten minutes.
I assumed moving work to the background made it simpler. It didn't. It just moved the complexity to a place where I couldn't see it.
Now I had to care about:
- What happens if the worker dies halfway?
- What happens if the job runs twice?
- How do I stop a runaway retry loop?
Async is powerful, but it forces you to handle failure states that simple request-response code never touches.
The Great Tutorial Lie
Here is the uncomfortable truth I had to accept: Tutorials optimize for the Happy Path.
They show you how to build the car. They don't teach you how to drive it in heavy traffic, in the rain, with a flat tire.
| Tutorials Teach | Real Production Demands |
| --- | --- |
| "Here's how to make it work." | "Here's how to keep it from breaking." |
| "Assume the database is always there." | "Assume the database will time out." |
| "Success is a 200 OK." | "Success is recovering from a 500 Error." |
| Speed | Stability |
The gap between "It works on my machine" and "It works in production" is where the actual engineering happens.
The Mental Shift
The biggest change wasn't learning a new framework or a better database. It was a change in psychology.
I stopped asking: "How do I build this feature?" And started asking: "How does this feature break?"
- "What if the network hangs here?"
- "What if the user clicks this twice?"
- "What if the database is locked?"
Backend development stopped being about "building endpoints" and started being about risk management.
Conclusion
I don’t think I’m a backend expert now. In fact, I feel like I know less than I thought I did two years ago.
But that humility is useful. It makes me check the logs. It makes me write tests for failure cases. It makes me respect the complexity of the systems we build.
If you’re feeling confident because you crushed a few tutorials, do yourself a favor: Build something real. Try to break it.
Because if you don't, your users will.